
MNO Core Network Solution Vendors: A Strategic Guide to Selecting the Right Partner
2026-05-13
Selecting the right core network vendor is one of the most consequential decisions a mobile network operator can make. The shift toward 5G, cloud-native architectures, and open networks has reshaped the landscape, offering opportunity but also uncertainty. With so many vendors claiming innovation, how do you find a partner that truly aligns with your technical roadmap and business goals? This guide cuts through the noise, providing a clear framework for evaluation. Among the players worth a close look is IPLOOK, a specialist in converged core network solutions that balances agility with carrier-grade performance. Whether you’re modernizing a legacy network or building a greenfield deployment, the choices you make now will define your competitiveness for years to come. Let's explore what truly matters when vetting MNO core network vendors.
Decoding Vendor Capabilities Beyond the Marketing Hype
Peeling back the glossy promises often reveals a gap between what vendors claim and what they actually deliver. Real capability isn't found in a slick demo or a grandiose mission statement—it lives in the quiet details, the edge cases their platform wasn't designed to handle, and the honest reflections of long-term clients who've weathered platform migrations. While every sales pitch highlights lightning-fast implementation and AI-powered everything, the true test comes when you ask how their tool performs under real-world data loads, compliance constraints, or integration with your legacy systems. Strip away the jargon and look for evidence of consistent problem-solving, not just bullet-point features that rarely leave the slide deck.
Another layer worth probing is the vendor's actual technical support culture. Many promise 24/7 availability but deliver tiered responses that only escalate once your patience has thinned. Listen for the stories that don't make it into case studies: how a support engineer walked a team through a custom fix at 2 a.m., or how the product team quietly deprecated a feature nobody used without fanfare. These signals matter more than any analyst quadrant or award badge. The firms that thrive long-term are those whose engineers seem genuinely curious about your problems, rather than those who default to scripted upsells whenever a question arises.
Finally, consider the roadmap and the vendor's appetite for transparency. Marketing decks love to promise a future packed with innovation, but a deeper look often shows a reactive feature pile driven by the loudest customer, not a clear vision. The best partners talk openly about what they're *not* building, and why, and they admit when a competitor does something better. They invite you into private beta tests without forcing an NDA for every conversation. In a landscape where every tool sounds revolutionary, the ones worth trusting are those comfortable enough with their own limits to let you see behind the curtain.
Architectural Flexibility as a Non-Negotiable Criteria
When a system’s architecture gets locked into early assumptions, even minor pivots turn into rewrites. Flexibility isn’t a luxury reserved for speculative features—it’s the difference between evolving with your users and fighting your own codebase. That’s why it belongs on the non-negotiable list, treated with the same weight as scalability or security. If a design can’t absorb a domain rule change without cascading into dozens of modules, it fails this criterion outright.
We’ve all seen projects where “temporary” workarounds became permanent constraints. A payment service that only understood one provider; a reporting module so tightly coupled to a specific database that migrating became a multi-quarter initiative. These aren’t edge cases—they’re the natural result of treating architecture as a one-time decision. Architectural flexibility means intentionally choosing seams where behavior can be swapped, not because you know what will change, but because you know something inevitably will.
Embedding this as a non-negotiable criteria changes design conversations. It forces teams to ask: can we replace this component without touching business logic? Are our interfaces defined by what the domain needs, or by what a library dictates? It turns “future-proofing” from a buzzword into a measurable property—you either can isolate change, or you can’t. And when the answer is “can’t,” it’s not a trade-off; it’s a design smell that deserves a rethink.
Long-Term Partnership Dynamics Over Transactional Deals
Shifting focus from one-off transactional exchanges to long-term partnerships changes the entire dynamic of business relationships. Rather than chasing immediate gains, both parties invest in mutual growth, fostering a sense of shared purpose that goes beyond quarterly targets. This approach encourages open communication and a willingness to adapt, creating a foundation where challenges are tackled collaboratively rather than defensively.
In a partnership-driven model, the measures of success evolve. It’s no longer just about price points or contract terms; it’s about reliability, innovation sparked through joint effort, and the quiet confidence that comes from knowing your partner has your back during turbulent times. Such depth transforms vendors into strategic allies, making the relationship itself a competitive advantage that’s hard to replicate.
Sustaining this dynamic demands consistency and emotional intelligence. It’s about showing up, not just when contracts are up for renewal, but through the messy middle of projects. When both sides prioritize the health of the partnership over short-term wins, trust deepens, leading to organic referrals, co-created solutions, and a resilience that isolated transactions simply can’t offer.
Navigating the Security and Compliance Maze
Steering through the complexities of security and compliance often feels like a puzzle where pieces keep shifting. Regulations differ across borders, and what meets standards today might fall short tomorrow, forcing teams to constantly adapt their strategies. The real challenge lies not just in checking boxes, but in weaving robust safeguards into everyday workflows without grinding innovation to a halt.
A practical approach starts with understanding that compliance isn’t a finish line—it’s an ongoing dialogue between your operations and evolving legal frameworks. By embedding automated checks and fostering a culture where every team member owns a slice of responsibility, organizations can turn a tangled web of requirements into a clear, manageable map. The key is to treat security not as a barrier, but as a backbone that supports growth while keeping data safe from ever-present threats.
The real-world payoff emerges when these practices become second nature, reducing last-minute scrambles during audits and building trust with clients who demand transparency. Instead of viewing the maze as a burden, see it as a chance to differentiate your business—where resilience and credibility speak louder than any certificate on the wall.
Commercial Models That Align With Your Growth Trajectory
Every business hits inflection points where the standard licensing or subscription blueprint feels like a hand-me-down coat—close, but never quite right. We’ve ditched the rigid playbook in favor of models that bend with your actual revenue curve. Whether you’re piloting a quiet launch or scaling across continents, our commercial terms adjust in lockstep. Think of it as a living agreement, not a relic sealed in a drawer.
The real magic sits in how we map pricing to outcomes, not just seats or storage. One quarter might call for usage-based tiers that reward early adoption; the next could shift toward shared-risk structures where our success depends wholly on yours. No arcane multipliers, no shelf-ware audits—just a clear path that lets your finance team sleep soundly while your engineers chase the next milestone.
By treating each engagement as a bespoke vest, we’ve helped bootstrapped teams avoid premature cash drains and enterprise units escape procurement purgatory. The common thread? A deliberate refusal to anchor on industry “norms” when your trajectory is anything but normal. Let the model serve the momentum, not the other way around.
Future-Ready Roadmaps: 5G Advanced and Beyond
The shift from 5G to 5G Advanced marks more than just a numeric upgrade—it redefines how networks learn, adapt, and serve in real time. Built on 3GPP Release 18 and onward, this phase weaves AI-driven orchestration directly into the radio and core, allowing infrastructure to anticipate demand rather than merely react. Far from a monolithic leap, it blends deterministic latency for industrial control, enhanced MIMO, and sidelink relays into a fabric that stitches together vehicles, sensors, and augmented reality glasses without the seams we tolerate today.
Looking past 5G Advanced, the six-generation frontier pushes into sub-terahertz bands, joint communication and sensing, and architectures that dissolve the boundary between physical and digital experience. This isn't about faster smartphones—it's about enabling digital twins that live alongside their real-world counterparts, powered by pervasive edge intelligence. Research into reconfigurable intelligent surfaces and cell-free topologies hints at a future where coverage becomes ambient, not something you search for, and where energy efficiency is baked into every layer of the protocol stack, not bolted on as an afterthought.
The roadmap also confronts a quieter challenge: how to evolve without breaking what already works. Backward compatibility remains a cornerstone, but so does the agility to shed legacy constraints when a use case demands it. Operators are sketching incremental rollouts that can flex from massive IoT to sub-millisecond haptics on the same infrastructure, leaning heavily on cloud-native cores and open interfaces. It’s a deliberate, uneven path—some industries will leap ahead while others creep—but the trajectory is unmistakably toward a network that feels less like a utility and more like a nervous system for the built world.
FAQ
Beyond the basic checklist, you need to scrutinize the vendor's track record in live deployments, especially at a scale similar to yours. Look at how they handle unexpected traffic surges and network slicing under real-world conditions. The quality of their technical support and the actual cost of ownership—including hidden integration and maintenance expenses—often matter more than the initial price tag.
It has forced a rethink of the entire evaluation framework. You can’t just compare feature lists anymore. You need to assess how cleanly the vendor has decoupled their software from hardware, the maturity of their containerized network functions, and whether their roadmap aligns with multi-vendor, hybrid-cloud environments. A vendor that treats cloud-native as a buzzword rather than a foundational principle will slow you down.
One common trap is getting dazzled by forward-looking promises that aren’t backed by demonstrable progress. Another is relying too heavily on RFPs filled with checkbox requirements that miss the operational nuances. Also, failing to involve your own network operations team early in the evaluation often leads to a mismatch between what’s bought and what can realistically be run day-to-day.
It’s absolutely central, yet often underestimated until problems surface. You need to test not just standard interfaces but also vendor-specific extensions under load. Insist on multi-vendor integration scenarios as part of the proof-of-concept stage. If a vendor can’t seamlessly work with your current RAN and OSS/BSS stacks, the long-term integration pain will outweigh any short-term feature advantages.
Security isn’t a box you tick at the end. You have to examine the vendor’s approach to securing signaling traffic, their vulnerability management practices, and how they handle lawful intercept requirements across jurisdictions. Ask for the results of recent third-party audits and their incident response track record. A vendor that isn’t transparent about security gaps is a liability waiting to happen.
Edge computing integration capabilities, support for network exposure functions that enable API-driven monetization, and the vendor’s readiness for AI/ML-based network optimization are reshaping what ‘modern’ means. Don’t just consider what’s needed today—look for a clear, practical path toward automated lifecycle management and network data analytics that can feed into your business strategy.
It’s less about picking a single vendor and more about architecting for flexibility. Prioritize solutions that allow you to start small and scale on demand, with licensing models that adapt as your business evolves. Insist on open APIs and avoid proprietary bindings that lock you into a fixed upgrade path. Sometimes, paying a moderate premium now for a truly modular system saves massive overhaul costs later.
Conclusion
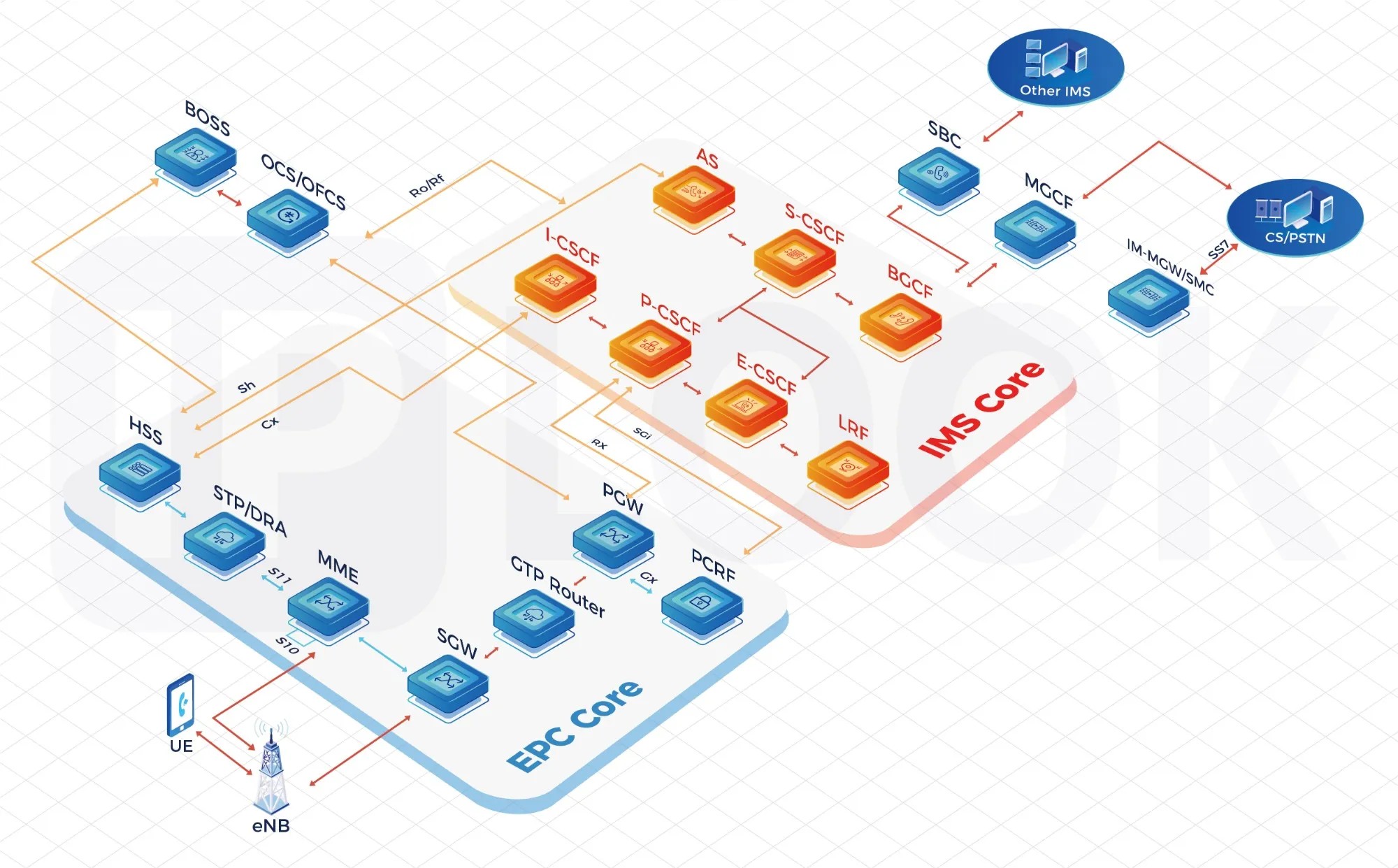
Selecting a core network vendor demands more than a feature checklist—it requires stripping away marketing narratives to uncover real engineering depth. Many providers tout cloud-native capabilities or AI-driven automation, but genuine differentiators emerge only when you scrutinize how those claims hold up under real-world load, multi-vendor interoperability, and unconventional deployment scenarios. Architectural flexibility isn’t a bonus; it’s an essential filter. A partner must demonstrate that their stack can evolve gracefully, from containerized microservices running on bare metal to hybrid edge configurations, without locking the operator into rigid blueprints. Equally critical is the relational fabric—opting for a supplier who treats the engagement as a collaborative journey rather than a one-time sale. This means transparent roadmaps co-developed with MNOs, shared innovation cycles, and a willingness to absorb early-stage risks. Without that symbiotic posture, even the most advanced technology stack becomes a liability when network demands shift.
Beyond the technical and relational layers, operators must navigate an increasingly tangled web of security mandates and regional compliance nuances. Vendors that merely bolt on perimeter defenses often miss the point; what’s needed is a security architecture woven into the entire control and user plane, with automated policy enforcement that adapts to zero-day threats. Similarly, commercial models should be instruments of growth, not constraints. Payment structures tied to network usage, subscriber growth metrics, or deferred 5G-Advanced rollouts can protect margins while incentivizing vendor accountability. Finally, the partner’s forward-looking vision matters intensely. Roadmaps aligned with 3GPP Release 18 and beyond—encompassing network slicing enhancements, AI/ML-native functions, and energy-efficient orchestration—reveal whether the vendor is merely catching up or genuinely shaping what’s next. A prudent choice weighs all these dimensions, anchoring decisions in long-term value rather than short-term feature parity.
Contact Us
Contact Person: Shimmy
Email: [email protected]
Tel/WhatsApp: 85253392231
Website: https://www.iplook.com

